Compliance & Risk Management
Simplify Compliance. Strengthen Governance. Reduce Risk.
Our Compliance & Risk Management services help you align with regulations like ISO 27001, NIS2 & NIST to manage risks effectively, and build a resilient security framework. We turn complex compliance requirements into clear, actionable strategies—empowering your business to stay secure and audit-ready.

Our Services
Cloyt Security helps organizations build a strong security foundation by aligning governance, risk, and compliance with leading global standards. Our experts guide you through frameworks such as ISO 27001, NIST, NIS2, and CIS, ensuring your business meets regulatory requirements while enhancing resilience. From policy development and risk assessments to compliance management and audit readiness, we provide tailored strategies that simplify complexity, reduce risk, and foster a culture of security and accountability.
ISO 27001 Implementation & Support
End-to-end support for building, implementing, and maintaining an Information Security Management System (ISMS)
- ISMS design & documentation
- Risk assessment & treatment plan
- Control implementation guidance
- Internal audit & certification readiness
- Ongoing compliance maintenance
NIS2 Readiness & Advisory
Prepare your organization to meet the EU NIS2 Directive requirements.
-
NIS2 gap assessment
-
Risk management measures implementation
-
Incident reporting framework setup
-
Executive & board-level compliance advisory
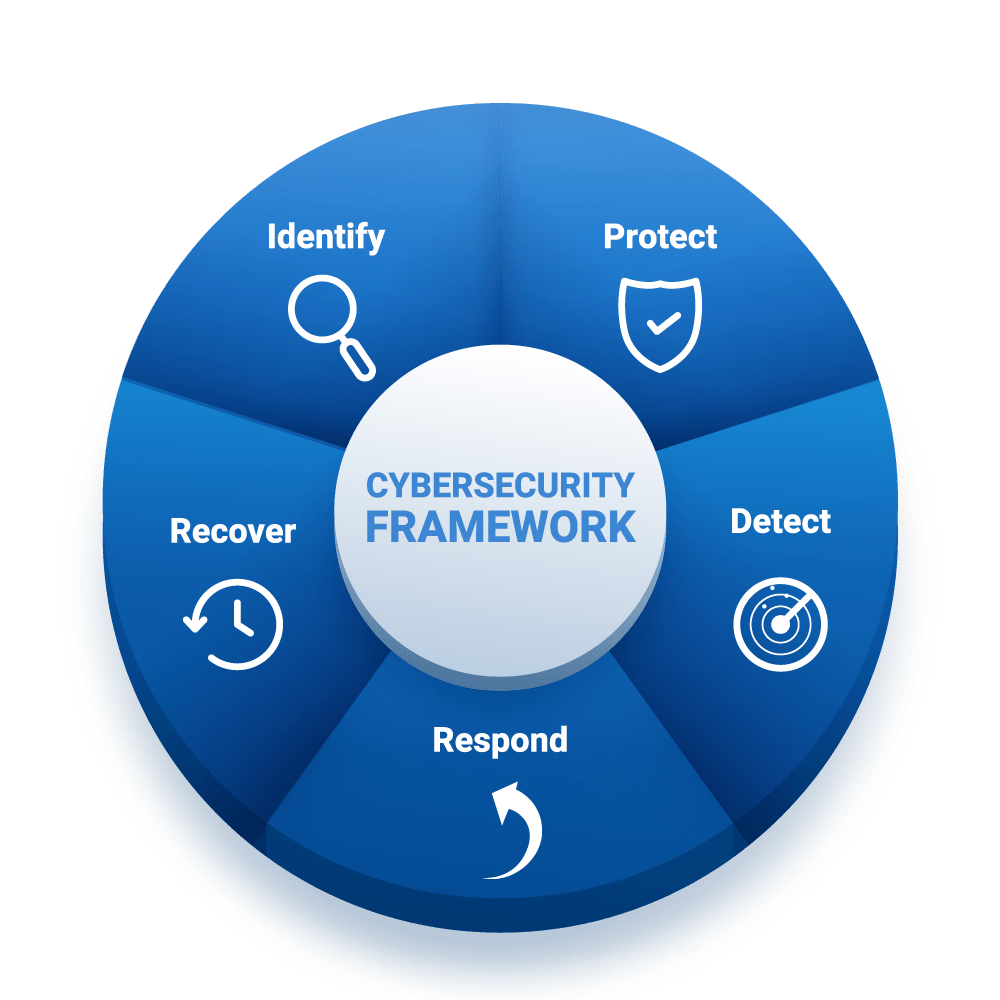
NIST Cyber Security Framework Alignment
Adopt globally recognized best practices for managing cybersecurity risk.
-
NIST CSF maturity assessment
-
Identify–Protect–Detect–Respond–Recover mapping
-
Control implementation guidance
-
Continuous improvement planning
CIS Control Implementation
Strengthen your baseline security posture with CIS prioritized safeguards.
-
CIS Controls gap analysis
-
Implementation roadmap
-
Security control validation
-
Ongoing effectiveness reviews
Risk Assessment & Management
Identify, evaluate, and mitigate security risks before they impact operations.
-
Enterprise risk assessments
-
Asset & threat identification
-
Business impact analysis (BIA)
-
Risk treatment & mitigation planning
Policy Development & Documentation
Build a strong governance foundation with clear and enforceable security policies.
Information security policies
-
Incident response plans
-
Business continuity & disaster recovery policies
-
Vendor & third-party risk policies
How It Works
At Cloyt Security, we follow a structured, outcome-driven approach to simplify compliance and strengthen your security posture.
Contact Us
info@cloytsecurity.com
1 Marina Park Drive Suite 1230, Boston, MA 02210, United States
Monday-Friday: 8am - 5pm
Get Started
Defend Your Business from Cyber Threats
